In this blog, we will do the Ansible Setup on AWS EC2 Instance with windows Nodes
Prerequisite of Ansible Setup
- Python
2. SSH
Three servers
Ansible control Server ( Install ansible using epel repository)- On AWS you have to enable this file
WebServer
DBServer
How to connect between these servers ?
To ping these servers(webserver and dbserver) from ansible control server , you have to add one inbound rule “All ICAMP traffic” in both the instances)
Step 1
Ansible Control Server
Install Ansible on AWSLinux
sudo yum update vim /etc/yum.repos.d/epel.repo
or
sudo yum-config-manager --enable epel
yum repolist ( you should see epel)
yum install ansible
Second Method of installing ansible
curl "https://bootstrap.pypa.io/get-pip.py" -o "get-pip.py"sudo python get-pip.pysudo pip install markupsafe sudo pip install xmltodict sudo pip install pywinrm
if getting sudo pip command not found
sudo env "PATH=$PATH" pip install pytz
sudo pip install ansible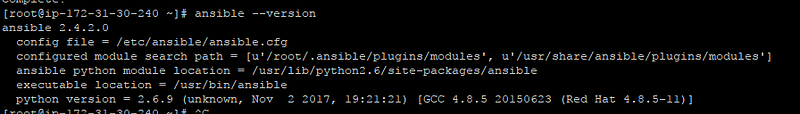
Ansible installed successfully.
Step 2:
Create a Windows EC2 Instance
Check ping command
Next make sure the Amazon network rules allow Echo Requests. Go to the Security Group for the EC2.
- right click, select inbound rules
- A: select Add Rule
- B: Select Custom ICMP Rule — IPv4
- C: Select Echo Request
- D: Select either Anywhere or My IP
- E: Select Save
- Added All traffic also
If ping doesn’t work, do the below step also
- Next, Windows firewall blocks inbound Echo requests by default. Allow Echo requests by creating a windows firewall exception…
- Go to Start and type Windows Firewall with Advanced Security
- Select inbound rules
Prerequisite
- Powershell 3.0 or higher should be installed. (Version 5 is present on AWS EC2 Windows instance). Check version using below command
$PSVersionTable.PSVersion2. WinRM setup on windows machine
script on the remote machine and then execute it in PowerShell console as an administrator.
powershell.exe -File ConfigureRemotingForAnsible.ps1
powershell.exe -File ConfigureRemotingForAnsible.ps1
Ansible Control Server
create folder named windowsplaybook using below command
mkdir windowsplaybook cd windowsplaybook/
create file named inventory by using command
vi inventory put in below content [web] Ip address of machine
Create File Named all in group_vars folder
Create folder named group_vars using mkdir group_vars
Create files named all using vi group_vars/all and put below contents
ansible_user: windows_username ansible_password: SecretPasswordGoesHere ansible_port: 5986 ansible_connection: winrm
# The following is necessary for Python 2.7.9+ (or any older Python that has backported SSLContext, eg, Python 2.7.5 on RHEL7) when using default WinRM self-signed certificates:
ansible_winrm_server_cert_validation: ignore
after this done please run below command to test if you are able to ping windows machine
ansible web -i inventory -m win_ping ansible web -i -i /home/ec2-user/windowsplaybook/inventory -m win_feature
Ansible control server connection with windows nodes is completed.
Now run some playbooks
Create a directory with file main.yml
mkdir /home/ec2-user/windowsplaybook/roles/basic/tasks vi main.yml ansible-playbook -i /home/ec2-user/windowsplaybook/inventory main.yml
[root@ip-10–0–0–20 tasks]# cat main.yml — - # YAML documents begin with the document separator — - # The minus in YAML this indicates a list item. The playbook contains a list # of plays, with each play being a dictionary - # Target: where our play will run and options it will run with hosts: all # Task: the list of tasks that will be executed within the play, this section # can also be used for pre and post tasks tasks: — name: Set a fact set_fact: our_fact: Ansible Rocks! - name: Install IIs WebServer win_feature: name: Web-Server state: present — name: Install IIS win_feature: name: Web-Mgmt-Tools, Web-Mgmt-Console, Web-Scripting-Tools, Web-Mgmt-Service state: present include_sub_features: no # Three dots indicate the end of a YAML document …